Lead the Way to Business Resilience
Netwerken | Ervaringen | Kennis | Contact
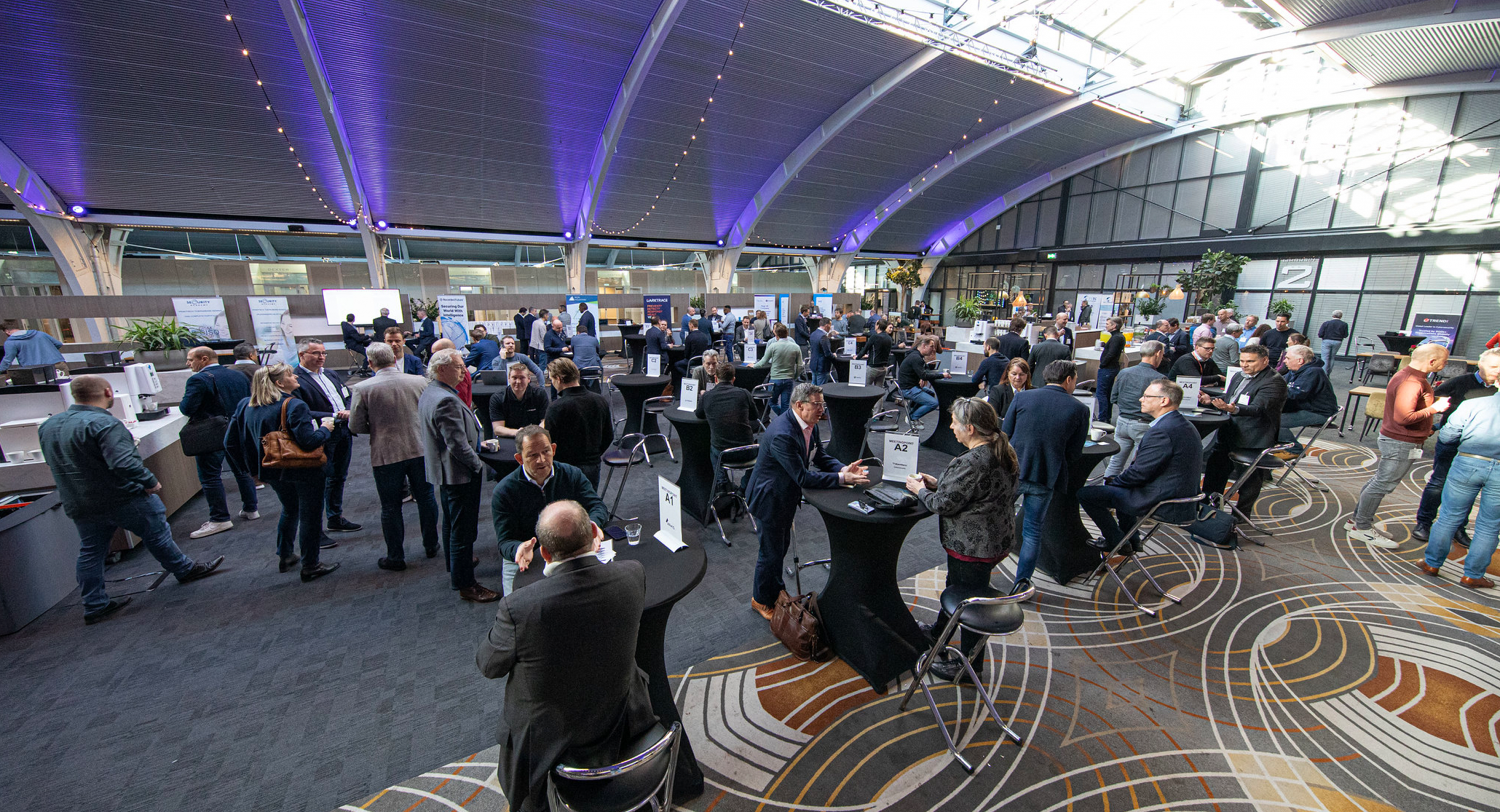
Security Leadership is hét strategisch security congres speciaal voor security managers en directie. De continu veranderende context waarin men opereert maakt dat uitdagingen complexer zijn dan ooit. Het congres toont de laatste ontwikkelingen op het gebied van security leiderschap en helpt jou om jouw security strategie op orde te krijgen en aan te scherpen. Het programma bestaat uit een mix tussen business en operations.
Bezoek samen met meer dan 150 vakgenoten het volledig verzorgde congres op dinsdag 6 februari. Stel je persoonlijk programma samen, netwerk met peers en voer 1-op-1 gesprekken met oplossingsaanbieders.

Een greep uit de sprekers

Douwe Groenevelt
Vice President & Deputy General Counsel at ASML

Marco Kroon
Ridder Militaire Willems-Orde en voormalig leidinggevende Korps Commandotroepen

Dr. Leila Taghizadeh
Global Head of Cyber Risk & CISO IberoLatAm van Allianz Group

Gemma Jansen
CISO van Provincie Noord-Holland
Security Leadership wordt mede mogelijk gemaakt door
Laatste nieuws
Blijf op de hoogte

Dit was Security Leadership 2024
Security Leadership 2025 Op 6 februari 2025 keert Security Leadership terug in Postillion Convention Center Utrecht in Bunnik. Zet het alvast in je agenda!

Whitepaper: Certified AI Governance Professional AIGP